
NETWORK
rustscan -a 172.31.1.9
Open 172.31.1.9:22
Open 172.31.1.9:80
Open 172.31.1.9:6379
nmap -sCV 172.31.1.9 -p22,80,6379
Starting Nmap 7.92 ( https://nmap.org ) at 2022-03-25 05:00 EDT
Nmap scan report for 172.31.1.9
Host is up (0.016s latency).
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.6p1 Ubuntu 4ubuntu0.3 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 32:22:88:22:9b:d2:76:c9:8c:ee:8a:4d:47:63:e5:14 (RSA)
| 256 d9:3f:c3:ee:a8:d4:36:c7:29:23:9f:e6:3d:dc:69:4b (ECDSA)
|_ 256 24:39:e3:a7:a7:f3:97:11:88:c7:c1:4b:25:f0:fc:c1 (ED25519)
80/tcp open http Apache httpd 2.4.29 ((Ubuntu))
|_http-title: Business Solutions
|_http-server-header: Apache/2.4.29 (Ubuntu)
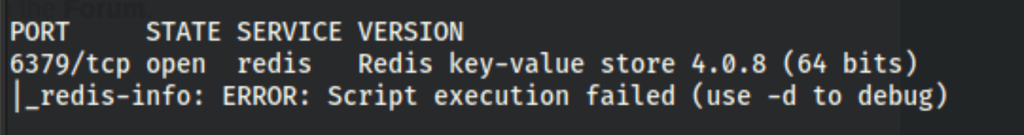
6379/tcp open redis Redis key-value store 4.0.8
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 20.23 seconds
ENUMERATION
Port 80
On port 80 we have a website, looks like a non customized template

Exploring Redis
We have Redis on port 6379
Using the redis-cli and the official documentation https://redis.io/docs/manual/cli/
We can enumerate the DB


Let’s get a list of all active configuration variables we can change

We can run many commands but not persist our changes

FOOTHOLD
Because we weren’t able to access the server via Redis - We went on to research on a better solution and find an exploit in Git https://github.com/Ridter/redis-rce.git
Using the exploit, we got access to the server


PRIV ESCALATION
Redis log analyse
 We can found an interesting script
We can found an interesting script
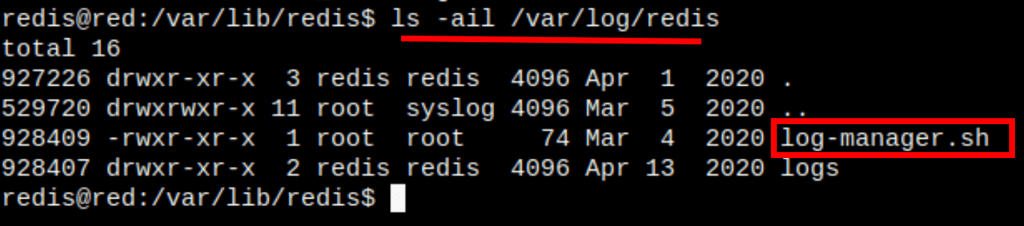
which run a command (as root) that runs the files in the logs/ folder as commands

Let’s create a reverse shell script

and upload it on the server in the folder logs/

A second after we get a shell on the server, tuns out the script runs on cron.
We get a reverse shell as root
